If you connect with your house wi-fi, that your id and knowledge can be protected against the surface world. How?
As a result of it has been assigned a safe IP handle.
An IP handle is a singular handle given to your gadgets so that an internet server acknowledges them and builds a safe reference to them. Units like laptops, cell gadgets, tablets, smartwatches, and different web gadgets all have a singular IP handle assigned by a router to share data throughout the similar community. IP handle intelligence instruments additionally allow you to browse assets on-line with out registering on a selected area.
Having a protected and accepted IP handle can shield your gadgets, cut back the scope of distributed denial of companies (DDOS) assaults, and make it troublesome for unethical hackers to hint your data through random web sites and networks that you just entry.
An IP handle is a singular identifier assigned to every machine on a community. It acts like a digital mailing handle, permitting gadgets to seek out and talk with one another on the web.
What’s an web protocol (IP) handle?
An Web Protocol (IP) handle is a technical handle assigned to every machine on a community. It acts like a digital mailing handle, permitting gadgets to seek out and talk with one another on the Web. Totally different gadgets have completely different IP addresses that masks the consumer’s id and register their personal or public gadgets on the community server for a easy transition of knowledge.
The precise IP handle could look one thing like this: 192.168.0.1. It’s a distinctive string of 0 to 255 characters assigned by your native web service supplier in order that your gadgets can work together with one another or different community servers to entry, retrieve, share, or handle knowledge. That you must be cautious of your community safety, maintain your IP addresses protected against malicious use, and handle vulnerabilities with ease.
IP addresses will be fastened or dynamic. Your router can assign you completely different IP addresses and reassign your previous IP handle to different web customers. That is achieved to safeguard consumer privateness and comply with the rules of web service suppliers in order that the scope of any IP handle getting hacked or replicated is minimal.
How does an IP handle work
IP addresses are vital for figuring out gadgets and routing acceptable web site visitors that will not hinder the safety of a selected community infrastructure. With new internet hosting instruments and IP internet hosting instruments, the web can now accommodate an enormous variety of IP addresses.
Listed here are the alternative ways wherein IP addresses work:
1. Addressing and Figuring out Units
Every machine on the server has a singular handle that distinguishes it from different gadgets. That handle permits gadgets to sync with a public or personal community, entry the online, or talk with different gadgets throughout completely different community servers.
2. Packetization and Information Switch
When knowledge is shipped to a community, it goes by way of your house or public router and a few encryption and cryptography protocols are added to the info your machine is making an attempt to ship. This is named knowledge packets. Every packet incorporates.
- Supply IP Deal with: The IP handle of the sender.
- Vacation spot IP Deal with: The IP handle of the recipient.
These packets are reassembled into the unique knowledge on the vacation spot.
3. Routing
Registering on an IP admin permits your router to route particular visitors and knowledge amongst completely different networks. For this, they use their very own particular person IP handle granted by the Web-assigned quantity authority (IANA) and a number of machine IP addresses to attach with server methods. This course of contains a number of steps.
Step-by-Step Routing Course of:
- Packet Creation: The sending machine creates a packet with the vacation spot IP handle.
- Native Community Routing:
- The packet first travels to an area router on the sender’s community.
- The router examines the vacation spot IP handle.
- Routing Desk Lookup:
- The router decides the place to ship the packet subsequent utilizing its routing desk, a database of paths.
- The routing desk additionally incorporates completely different IP addresses and is tasked with delegating knowledge effectively throughout the “than energetic IP handle” to avoid wasting registration and porting prices.
- Throughout the routing desk stage, the router directs web site visitors and permits customers to share data by way of file transmission protocol (FTP).
- Forwarding:
- The router forwards the packet to the following router within the path.
- This course of continues, with every router inspecting the IP handle and forwarding the packet accordingly.
- Vacation spot Community:
- The packet reaches a router on the vacation spot community. It’s then decrypted to ship the unique message that the sender’s IP handle had created.
- This router forwards the packet to the ultimate machine, utilizing ARP (Deal with Decision Protocol) to map the IP handle to the machine’s bodily MAC handle.
4. Subnetting
Subnetting is a means of dividing the capability of mainframe servers, WiFi servers, and firm servers into smaller chunks that may register the IP handle and permit easy knowledge transmission. Every subnet has its handle vary.
- Environment friendly IP Deal with Administration: Conserves IP addresses by utilizing them extra effectively.
- Enhanced Safety: Limits the published area, decreasing the danger of network-wide assaults.
- Improved Efficiency: Reduces community congestion by limiting visitors to inside subnets.
Tip: A subnet masks accompanies an IP handle as a measure of safety. This masks is used to outline community and internet hosting suppliers and permit entry to searching knowledge.
For instance, within the IP handle 192.168.1.10 with a subnet masks of 255.255.255.0:
- Community Half: 192.168.1
- Host Half: 10
5. NAT (Community Deal with Translation)
NAT permits a number of gadgets on a personal community to share a single public IP handle. The gadgets even have particular person personal IP addresses and share the router’s frequent public IP handle. It’s used for the next causes.
- Interprets: Public IP addresses enable web site visitors to stream from the principle public server to particular person personal or VPN servers
- Maintains: A desk of energetic connections to route incoming visitors again to the right personal IP handle.
6. DNS (Area Identify System)
DNS interprets human-readable domains (e.g., www.instance.com) into IP addresses (e.g., 93.184.216.34). This enables customers to hook up with web sites utilizing easy-to-remember names as a substitute of numerical IP addresses.
DNS Decision Course of:
- Question: The consumer enters a site title within the browser.
- DNS Lookup: The question is shipped to a DNS server.
- Response: The DNS server responds with the corresponding IP handle.
- Connection: The browser makes use of the IP handle to ascertain a reference to the online server.
Instance of an IP handle working methodology
Right here is an instance of IP handle working methodology whereas sending an e mail out of your personal web connection to the principle e mail server.
Sending an E mail
For instance these ideas, take into account sending an e mail from one consumer to a different:
- E mail Composition: Person A composes the e-mail and hits ship.
- Cryptography: A personal IP handle marks the e-mail as “Packet A” and encrypts it earlier than sending it to a public or personal router. The router accepts the IP supplier and, utilizing file transmission protocol (FTP) sends the message to the e-mail server.
- E mail server vacation spot: The e-mail server accepts the incoming visitors, breaks the message into packets and analyzes the IP handle of consumer A (supply handle), and Person b’s e mail server (vacation spot IP handle).
- Routing: The packets journey by way of native routers of consumer A and consumer B, every forwarding them in direction of Person B’s e mail server based mostly on their IP handle.
- Last Supply: The e-mail server reassembles the packets and delivers the e-mail to Person B’s inbox.
This detailed workflow explains how the community visitors flows easily from supply to vacation spot inside a singular community or throughout a number of networks.
Kinds of IP addresses
There are numerous variations of IP addresses that you’d be granted based mostly in your community supplier. The features of IP addresses differ based mostly on residence streaming networks and workplace networks. Listed here are a few IP addresses that your native ISPs can grant entry to:
- IPv4: IPv4 is the fourth model of web protocol that your internet hosting supplier can grant you. It makes use of a 32-bit handle format, which permits for about 4.3 billion distinctive IP addresses. It’s an environment friendly and safe type of web protocol that companies have been utilizing for a really very long time for personal and public networks.
- IPv6: That is the newest model of the Web protocol that makes use of a 128-bit handle format and can be utilized for static and dynamic IP handle verifications. It was developed to deal with the challenges of IPv4 and host a rising variety of web gadgets.
- Non-public IP: Non-public IP addresses are perfect for residence networks and personal streaming fiber companies. Every digital machine is assigned a personal IP handle that may be shared throughout public web sites, prompt messaging apps, and different data-sharing platforms. A personal IP handle adjustments if you depart your house community and would not keep fastened, as you is likely to be quickly registered on a public server IP handle based mostly in your location.
- Public IP: Public IP addresses are frequent in workplace infrastructures, as the corporate server has to take care of the accuracy of knowledge for all computing gadgets listed on the server. A public IP handle lets you attain the Web straight with none router interference and directs web site visitors on to your net account.
- Client IP: These are IP addresses of people who both make money working from home or enterprises that run native space community (LAN) or vast space community (WAN) servers. Usually, the gadgets use personal IP handle inside a selected community and public IP handle outdoors the community.
- Web site IP: These IP addresses are assigned by internet hosting suppliers, who distribute visitors amongst net browsers. Web site IP addresses will be public or personal, relying on how a lot visitors is allotted to your machine and the knowledge you share on the Web.
- Dynamic IP: Dynamic IP is a kind of web site IP handle that’s assigned based mostly on internet hosting protocol and adjustments every time a server is related to a community. Dynamic IP is an effective way to guard your community towards cyberattacks because the handle adjustments regularly, which reduces the potential of knowledge theft.
- Static IP: Static IP addresses all the time stay fixed even when the consumer switches networks. It’s a fastened IP handle that does not change. Companies use static IP addresses because it helps in a simple, safe sockets layer (SSL certification) and a protected atmosphere.
Consider your IP handle as your house handle. In the identical approach that your road handle permits the mail service to seek out your house and ship your mail, your IP handle is how your server is ready to discover your machine among the many billions of others which might be related to it.
There are 4 simple strategies of discovering what your IP handle is, so let’s get began with the primary one.
Discover your IP handle utilizing Google
In all probability the best and easiest method to discover your IP handle is to Google it.
I do know, you’re in all probability considering how does Google know my IP handle? Nicely, it’s as simple as looking out “What’s my IP handle” within the Google search bar.
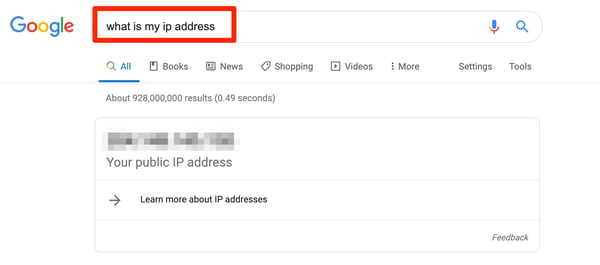 |
Voila! No matter quantity pops up right here is your IP handle.
Discover your IP handle in your Mac
Not everyone seems to be within the best method to do one thing, and that’s completely tremendous! Let’s discover learn how to discover your IP handle in your Mac.
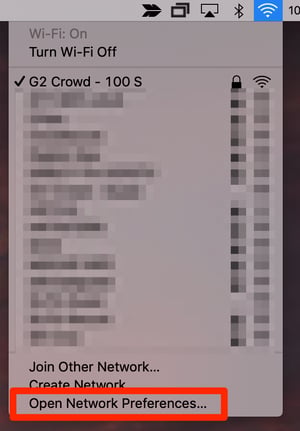
First, click on on the high of your display the place your Wi-Fi bars are and click on Open Community Preferences.

The following display will present you which ones Wi-Fi community you’re related to. Instantly below Standing can be your IP handle.
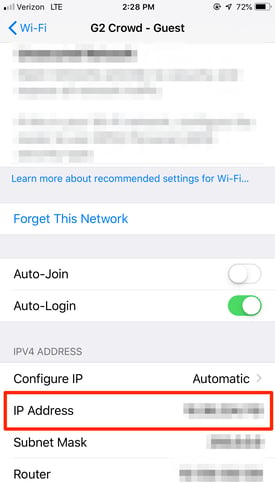
Discover your IP handle in your iPhone
In your iPhone and in want of your IP handle? From Settings, choose the Wi-Fi community you’re related to.
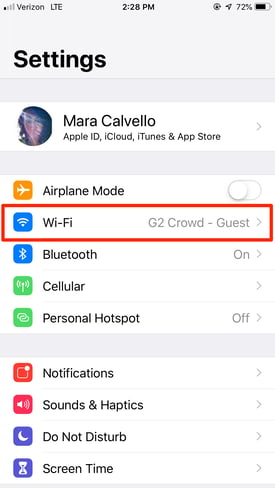
Subsequent, faucet the Wi-Fi community once more to see extra data.
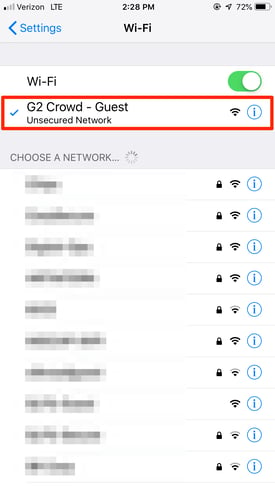
On the backside of this subsequent display, you’ll discover your IP handle.
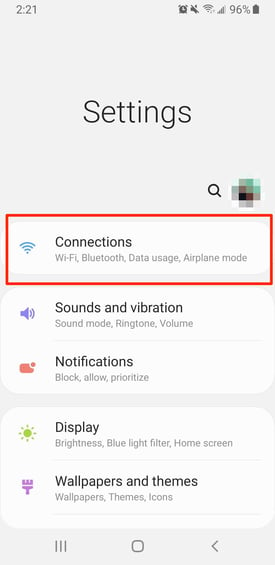
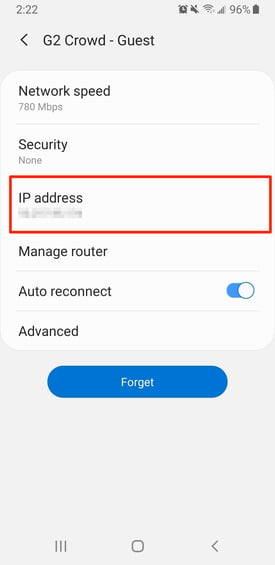
Discover your IP handle in your Samsung Galaxy
I do know, I do know… not everybody has an iPhone, which is why I’ve Samsung Galaxy customers lined, too.
From the Setting display, faucet Connections.
Then, faucet the place your Wi-Fi community is listed.
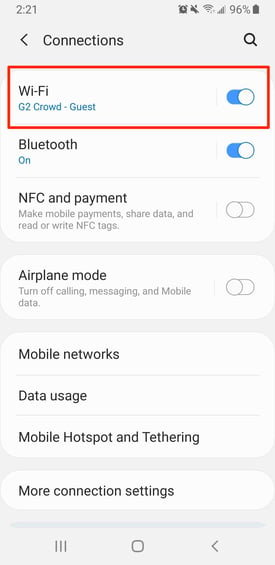
From the following display, choose your Present Community.
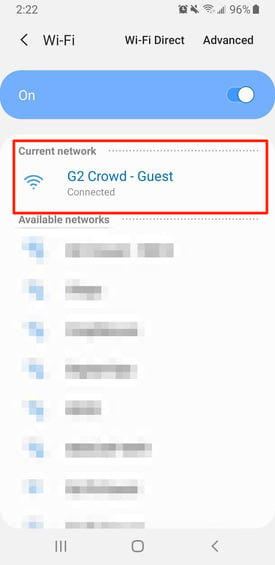
This subsequent display will present you extra details about your Wi-Fi community, together with your IP handle.
IP addresses and cyber safety
Now that your IP handle, have you ever ever thought why you must know what your IP handle is? And why it’s vital from a cyber safety standpoint that you must maintain it a secret (therefore these blurred out screenshots)? Nicely, that’s easy, too.
If a hacker has entry to your private or firm IP handle, they’ll doubtlessly harm the community.
As an example, as soon as somebody is aware of your IP handle, they’ll replicate it and obtain unlawful content material that may trigger points together with your web supplier and even one thing a lot bigger, like instigating a DDoS assault to flood your server with faux visitors.
It’s additionally vital to think about that in case your IP handle falls into the palms of a hacker who is aware of the internal workings of geolocation know-how, they’ll observe down the bodily location of your organization’s workplace, your house, and the entire related gadgets.
Protecting your IP handle safe is only one motive to spend money on top-notch cyber safety suppliers. In the event you’re not sure which one could be greatest on your firm, take a look at our complete record and all the things you could find out about your choices.
Safety threats of IP handle
As a lot as IP addresses safe your web connections, they pose a critical risk of undesirable assaults. Hackers can simply get your addresses from web sites you go to. Web sites retailer consumer knowledge and searching habits within the type of cookies, making your IP handle weak to viruses.
With this data, hackers can know your location, cross-verify it with “IP location,” and keep watch over your actions. Though this won’t be your fault, however it may well carry you to the eye of legislation enforcement. Listed here are alternative ways wherein an unprotected IP handle can hurt you:
- Phishing: Phishing emails are fairly frequent. Hackers maliciously exploit your IP handle to create phishing feeds and ship dangerous e mail hyperlinks within the hope of acquiring your consumer ID and password. Phishing will be stopped by deploying a firewall, proxy server, or VPN server that hides your IP handle and acts as a third-party community supplier between you and your router.
- Distributed Denial of Service (DDOS) assaults: When hackers know your IP handle, they ship your credentials to a number of unauthorized methods, which in flip flood the focused system with contaminated visitors. This shuts down your web connection fully and infects your methods with spy ware and viruses.
- Cyberattacks: Cyberattacks brought on by a compromised IP handle can encourage attackers to spoof your DNS and redirect your community visitors to their community. They’ll disrupt community communication and steal knowledge as soon as and for all.
- Bulk advert concentrating on: If you share your IP handle over a messaging app or a search engine web site, the web site shops your knowledge and forwards it to advertisers that use personalised advert concentrating on to lure you. The adverts might sound oddly private, as a result of they’re!
Keep throughout the secure partitions
Making certain you comply with the right knowledge safety and knowledge piracy practices together with your IP internet hosting supplier can maintain these unwarranted attackers at bay. All the time use an excellent firewall safety, antivirus system, or cybersecurity software program to make sure secure searching and a seamless knowledge trade expertise.
Now that all the things about an IP handle, study to double-pack your cybersecurity with the best-managed DNS supplier software program in 2024
This text was initially printed in 2019. It has been up to date with new data.

